This story was delivered to BI Intelligence “Payments Briefing” subscribers.
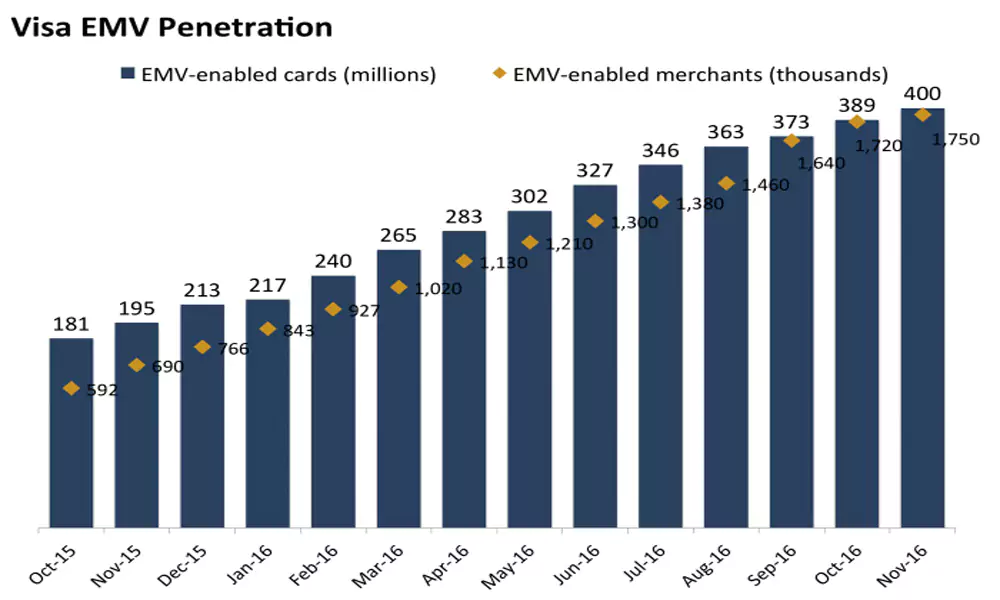
In its monthly EMV update, Visa announced that chip-enabled merchants now account for 46% of the company’s in-store payment volume.
The firm also saw over 800 million chip-on-chip transactions in November, up 359% year-over-year (YoY).
The numbers point to rising EMV penetration across the US, but are also significant because, as the largest US card network, Visa’s figures could serve as a benchmark for the progression of the US EMV migration across the industry,
Rising chip transactions points to growing adoption and buy-in from consumers and merchants alike.
- Consumers: Visa has now issued just under 400 million chip cards in the US, marking a 105% YoY increase. For context, that’s roughly 47% of Visa’s total US cards. And consumers seem to be adjusting to the changes that chip cards bring, like dipping rather than swiping — a separate Visa survey found that 35% of consumers, the highest percentage in the survey, believe chip cards are the safest way to pay.
- Merchants: Merchant adoption continues to rise, though it’s slowing — 1.75 million Visa merchants now accept chip cards, up by 110,000 since the previous quarter and over 1 million since last November. That’s still just 38% of US storefronts, but represents a significant figure of transaction volume because most major merchants accept EMV cards. As more small businesses warm to the idea of EMV and upgrade their readers, likely because of the fraud protection benefits they can reap, it’s likely this figure will continue to rise steadily. However, Visa and other networks recently delayed the migration for gas stations, somewhere that cards are used regularly and locations that see high fraud, by three years, which could continue to impact merchant upgrades.
That could have a big impact on transaction safety in the US. The US EMV migration continues to be slow going — for the year ending in Q2 2016, just 7% of transactions overall in the US were chip-on-chip, according to data from EMVCo. And though Visa’s numbers point to a slowdown in both merchant and customer uptake, it’s likely we’ll see steady growth that will lead to another considerable jump in overall EMV penetration in late 2016 and early 2017. And that could help reduce fraud, which is still high in the US, and make card-present transactions as safe as possible, even as in-store retail remains popular.
Fraud cost U.S. retailers approximately $32 billion in 2014, up from $23 billion just one year earlier. To solve the card fraud problem across in-store, online, and mobile payments, payment companies and merchants are implementing new payment protocols that could finally help mitigate fraud.
John Heggestuen, senior research analyst for BI Intelligence, Business Insider’s premium research service, has compiled a detailed report on payment security that looks at how the dynamics of fraud are shifting across in-store and online channels and explains the top new types of security that are gaining traction across each of these channels, including on Apple Pay.
Here are some of the key takeaways from the report:
- EMV cards are being rolled out with an embedded microchip for added security. The microchip carries out real-time risk assessments on a person’s card purchase activity based on the card user’s profile. The chip also generates dynamic cryptograms when the card is inserted into a payment terminal. Because these cryptograms change with every purchase, it makes it difficult for fraudsters to make counterfeit cards that can be used for in-store transactions.
- To bolster security throughout the payments chain encryption of payments data is being widely implemented. Encryption degrades valuable data by using an algorithm to translate card numbers into new values. This makes it difficult for fraudsters to harvest the payments data for use in future transactions.
- Point-to-point encryption is the most tightly defined form of payments encryption. In this scheme, sensitive payment data is encrypted from the point of capture at the payments terminal all the way through to the gateway or acquirer. This makes it much more difficult for fraudsters to harvest usable data from transactions in stores and online.
- Tokenization increases the security of transactions made online and in stores. Tokenization schemes assign a random value to payment data, making it effectively impossible for hackers to access the sensitive data from the token itself. Tokens are often “multiuse,” meaning merchants don’t have to force consumers to re-enter their payment details. Apple Pay uses an emerging form of tokenization.
- 3D Secure is an imperfect answer to user authentication online. One difficulty in fighting online fraud is that it is hard to tell whether the person using card data is actually the cardholder. 3D Secure adds a level of user authentication by requiring the customer to enter a passcode or biometric data in addition to payment data to complete a transaction online. Merchants who implement 3D Secure risk higher shopping-cart abandonment.
In full, the report:
- Assesses the fraud cost to US retailers and how that fraud is expected to shift in coming years
- Provides 5 high-level explanations of the top payment security protocols
- Includes 7 infographics illustrating what the transaction flow looks like when each type of security is implemented.
- Analyzes the strengths and weakness of each payment security protocol and the reasons why particular protocols are being put in place at different types of merchants.
To get your copy of this invaluable guide, choose one of these options:
- Subscribe to an ALL-ACCESS Membership with BI Intelligence and gain immediate access to this report AND over 100 other expertly researched deep-dive reports, subscriptions to all of our daily newsletters, and much more.
- Purchase the report and download it immediately from our research store.
The choice is yours. But however you decide to acquire this report, you’ve given yourself a powerful advantage in your understanding of payments security.